Any Transport over MPLS (AToM) will transport layer 2 frames over a MPLS (Multiprotocol Label Switching) network. This will allow service providers to connect layer 2 networks of customers transparently by using their MPLS backbone. AToM can transport the following:
- ATM AAL5
- ATM Cell Relay
- Ethernet
- Frame Relay
- PPP
- HDLC
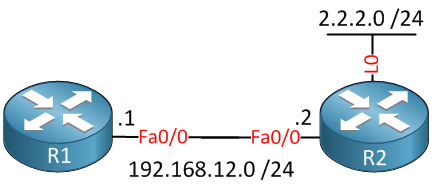
I will give you an example how to configure AToM to transport Ethernet over the MPLS backbone, we will use the following topology to do this:
Above you see a small MPLS backbone that consists of the PE1, P and PE2 router. This ISP only has one customer that has a HQ and Branch. The customer wants to have the HQ and Branch router to be in the same layer 2 segment.